Ledger Login: The Gateway to Secure Crypto Management
Learn everything about accessing your Ledger account securely, managing your crypto portfolio, and protecting your digital wealth through proper Ledger login practices.
Introduction to Ledger Login
When it comes to cryptocurrency management, security is the cornerstone of trust. The Ledger login process serves as the first step to unlocking the world of digital assets while maintaining complete control and protection. Ledger, a global leader in crypto hardware wallets, ensures that your keys never leave your device, keeping your crypto safe from online threats and phishing attacks.
In this article, we’ll explore the entire process of logging in to your Ledger account, using the Ledger Live app, common troubleshooting tips, and best practices to safeguard your crypto journey.
Why Ledger Login Matters
Logging in to your Ledger account is not just about accessing your dashboard — it’s about maintaining your ownership and ensuring that no one else can manage or manipulate your assets. Unlike typical logins where credentials are stored in the cloud, Ledger login uses hardware-based verification and PIN-protected authentication to ensure maximum safety.
- Private Key Protection: Your keys remain inside the Ledger device, isolated from online threats.
- Two-Factor Authentication: Physical confirmation on the device ensures secure transactions.
- Multi-Asset Management: Access, track, and manage over 5,500 cryptocurrencies from one secure interface.
- Cold Storage Benefits: Assets are stored offline, beyond the reach of hackers.
Step-by-Step Guide to Ledger Login
To begin your Ledger journey, follow these simple steps to securely access your account:
Step 1: Connect Your Ledger Device
Plug your Ledger Nano X or Nano S device into your computer or connect via Bluetooth for wireless access. Make sure your device firmware is up-to-date for seamless login and security improvements.
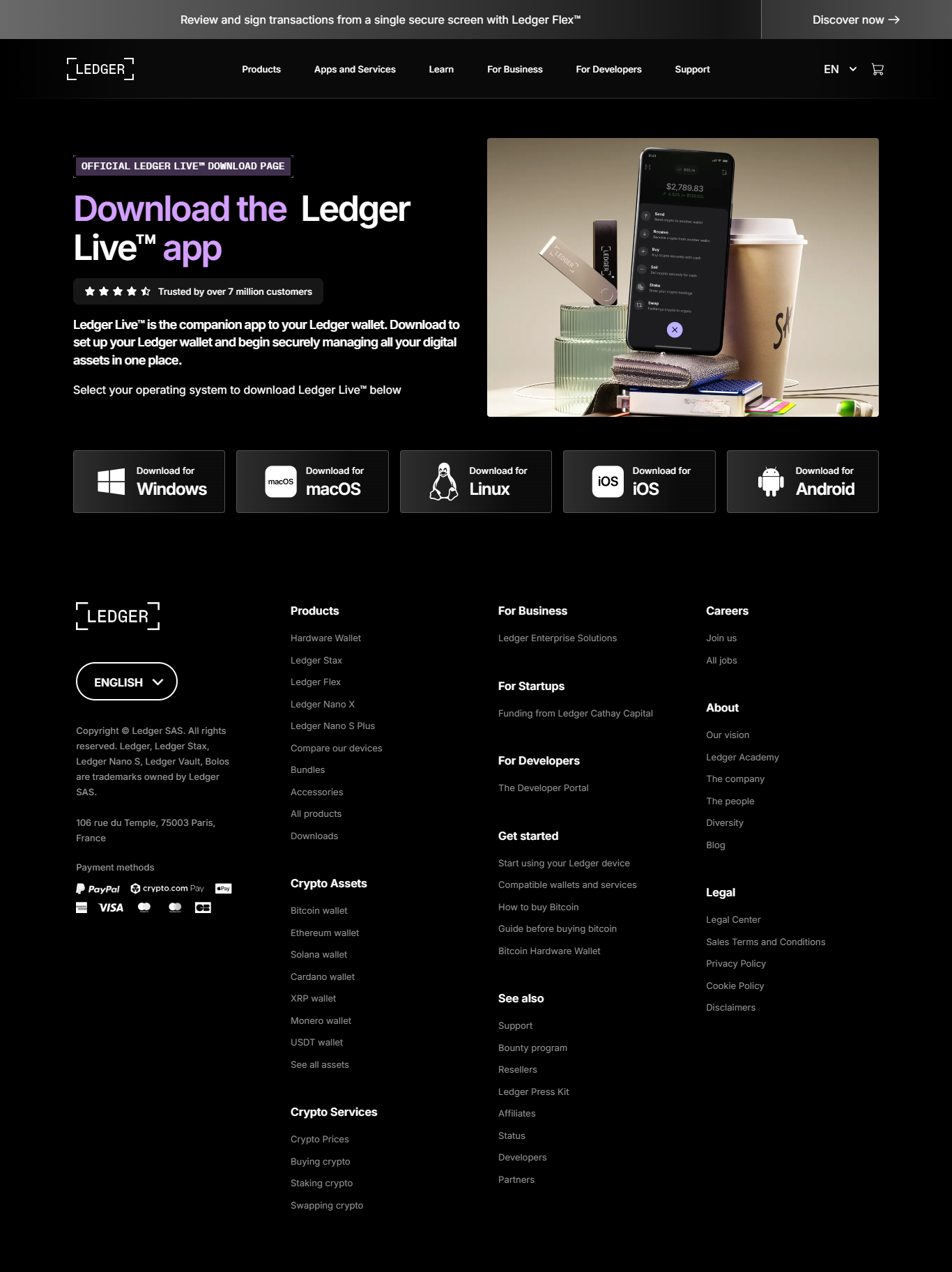
Step 2: Open Ledger Live
Launch the Ledger Live application on your computer or smartphone. This is your official interface for portfolio management, firmware updates, and account overview.
Step 3: Enter Your PIN
Using your Ledger device, enter your personal PIN. This PIN is your primary layer of protection against unauthorized access. Always keep it private and avoid sharing it.
Step 4: Access Your Dashboard
Once authenticated, Ledger Live will display your portfolio, recent transactions, and available apps. You can now safely manage your crypto assets or initiate new transactions.
Ledger Login Security Insights
Ledger’s architecture revolves around the concept of zero trust. Even if your computer is compromised, the hardware wallet remains a secure vault that protects your private keys. The Ledger Live interface simply reads information from the blockchain without ever exposing your private credentials online.
“Your Ledger device is not just a wallet — it’s a fortress for your digital future.”
Additionally, Ledger integrates Secure Element chips — the same technology used in passports and credit cards — to protect sensitive data. Combined with the BOLOS operating system, Ledger ensures complete isolation of each app on the device, preventing cross-access vulnerabilities.
Ledger Login vs. Software Wallet Access
When comparing Ledger’s login mechanism with regular software wallet logins, the difference in security becomes evident. Here’s a simple comparison:
| Feature | Ledger Login | Software Wallet Login |
|---|---|---|
| Private Key Storage | Stored offline on hardware device | Stored locally or in cloud-based systems |
| Authentication Method | PIN + Physical Confirmation | Password or Recovery Phrase |
| Security Risks | Minimal, even if connected to infected device | High risk from malware, phishing, or keyloggers |
| Transaction Verification | Confirmed directly on the Ledger device | Verified through app interface only |
Troubleshooting Ledger Login Issues
Sometimes, users might face issues while trying to log in to their Ledger account. Here are the most common problems and quick fixes:
- Device Not Recognized: Try another USB port or cable. Ensure Ledger Live is up-to-date.
- Incorrect PIN: Be cautious. Three wrong attempts can reset your device.
- App Not Syncing: Reconnect your device and restart Ledger Live to refresh blockchain data.
- Firmware Outdated: Regularly update firmware through Ledger Live for new security patches.
FAQs About Ledger Login
1. Can I log in to Ledger without my device?
No, you cannot. The device is mandatory for authentication because your private keys never leave it. This ensures that no one else can access your funds without physical access to your Ledger wallet.
2. What if I forget my PIN?
If you forget your PIN, you can reset your device using your 24-word recovery phrase. Always store this phrase securely offline.
3. Is Ledger Live safe to use?
Yes, Ledger Live only displays information and signs transactions via your hardware wallet. It never accesses your private keys directly.
Conclusion: Your Crypto, Your Control
Mastering the Ledger login process is an essential step in taking true ownership of your digital assets. With Ledger’s unmatched security model, hardware-backed authentication, and user-friendly Ledger Live interface, you’re not just managing crypto — you’re safeguarding your financial freedom. Always verify every transaction, keep your device updated, and remember — your keys, your crypto.